Effective analysis starts with the essential questions “who, what, when, where, why, and how” – that convert data into intelligence. In many ways, these same pillars define the discipline of Threat Intelligence (TI). What started as a niche task of collecting indicators of compromise has grown into a much broader discipline. Depending on the SOC, the work can range from simple feed ingestion and enrichment to deeper research, malware analysis, and even producing original intelligence at the enterprise, CERT or national level.
TI works best when it’s built into Security Operations. That integration turns the SOC from a reactive monitoring unit into an intelligence-driven defense capability. At its core, an intelligence-driven SOC uses TI not as an occasional feed but as the central nervous system for all SOC decisions. At higher maturity levels (three to five in most SOC capability models), TI becomes deeply embedded in daily workflows: influencing detection engineering, informing threat hunting and enriching incident response.
Detection engineering, hunting, automation and data enrichment
Raw security alerts and indicators often lack meaning on their own – they are just data points and threat intelligence adds extra details analysts need to understand: why, who and what is behind an alert. When the SOC moves from alert-centric triage to intelligence-led decisions, a cultural shift occurs: analysts stop reacting to isolated events and start interpreting them in context. For example, a suspicious IP becomes far more valuable when TI reveals: its geolocation, associated malware families, whether it is part of a known C2 or botnet cluster, links to past campaigns, whether similar entities targeted peers in a customer’s industry, etc. A malware alert tied to a known APT is no longer “just another alert” – it could be the start of an adversary’s campaign.
This shift reshapes day-to-day operations and embeds intelligence across core SOC functions:
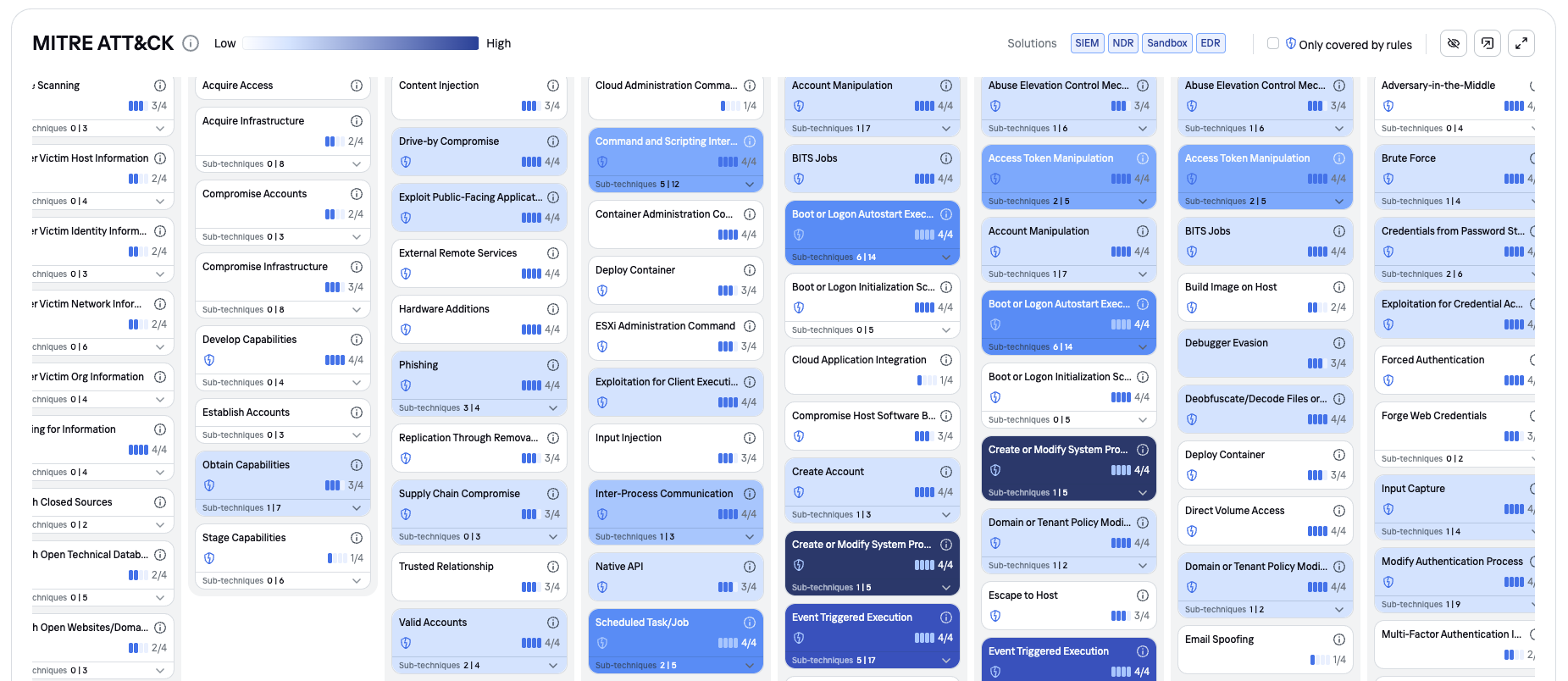
- Detection engineering prioritizes coverage of the most relevant techniques identified through TI – translating attacker tactics and techniques into SIEM correlation rules, analytics and signatures.
- Threat hunters develop hypotheses from emerging campaign reports or actor-specific behaviors – searching for traces long before an alert fires.
- SOC automation (including SOAR-style workflows) enriches alerts with intelligence and even takes action on its own like blocking a C2 IP or isolating a suspicious host via EDR.
To enrich the data from alerts and indicators, TI Platforms (TIPs) automatically match context from internal telemetry (SIEM, XDR, EDR, NDR) and external sources (feeds, vendor intelligence, CERT). Take outbound HTTPS traffic: it usually looks fine. After enrichment, though, you might notice a JA3 fingerprint linked to TrickBot C2 and a domain that isn’t active anymore but was involved in that campaign. With that context, the traffic doesn’t look so innocent anymore.
Alert triage and prioritization
One of the constant challenges for SOCs is alert overload when there are thousands of alerts of varying importance, with many false positives. In this case, the net effect of TI is a reduction of noise, which results in the situation when an alert comes in, the analyst’s first intention is not to immediately react to all the events at once, but to ask the question: “Do we need to care now?”
For example, a phishing alert tied to a nation-state actor targeting your industry deserves immediate escalation, because the relevance (your sector is at risk) and severity (espionage) make it a high priority. On the contrary, identical technical alerts might be far less concerning if the intel shows the source is a generic crimeware campaign that typically targets individuals. Or, for instance, if a burst of outbound DNS requests suddenly appears from a production server, the SIEM might initially flag it as potential data exfiltration. However, TI enrichment can show that these domains belong to the update servers and alert severity can be downgraded.
Also, while many cyber threats are universal, each industry faces unique threat landscapes and thus benefits from tailored threat intelligence. For instance, TI in finance might include intelligence on payment fraud schemes – such as lists of mule accounts or phishing sites mimicking bank login pages. Other sectors have their own specifics too: Energy/utilities may pay close attention to nation-state threats and malware targeting ICS environments.
Threat actor profiling and attribution
A solid TI program helps you understand the threat landscape – who the major actors are, what they want and how skilled they are. If an alert is linked to known APT, even a low-severity technical signal deserves high suspicion due to high potential impact. A common method for profiling actors is mapping incidents to MITRE ATT&CK knowledge base and reviewing how effectively the defenses address them.
Attackers often reuse tools and plant false flags, but attribution still helps to understand the motives and decide how to better respond.
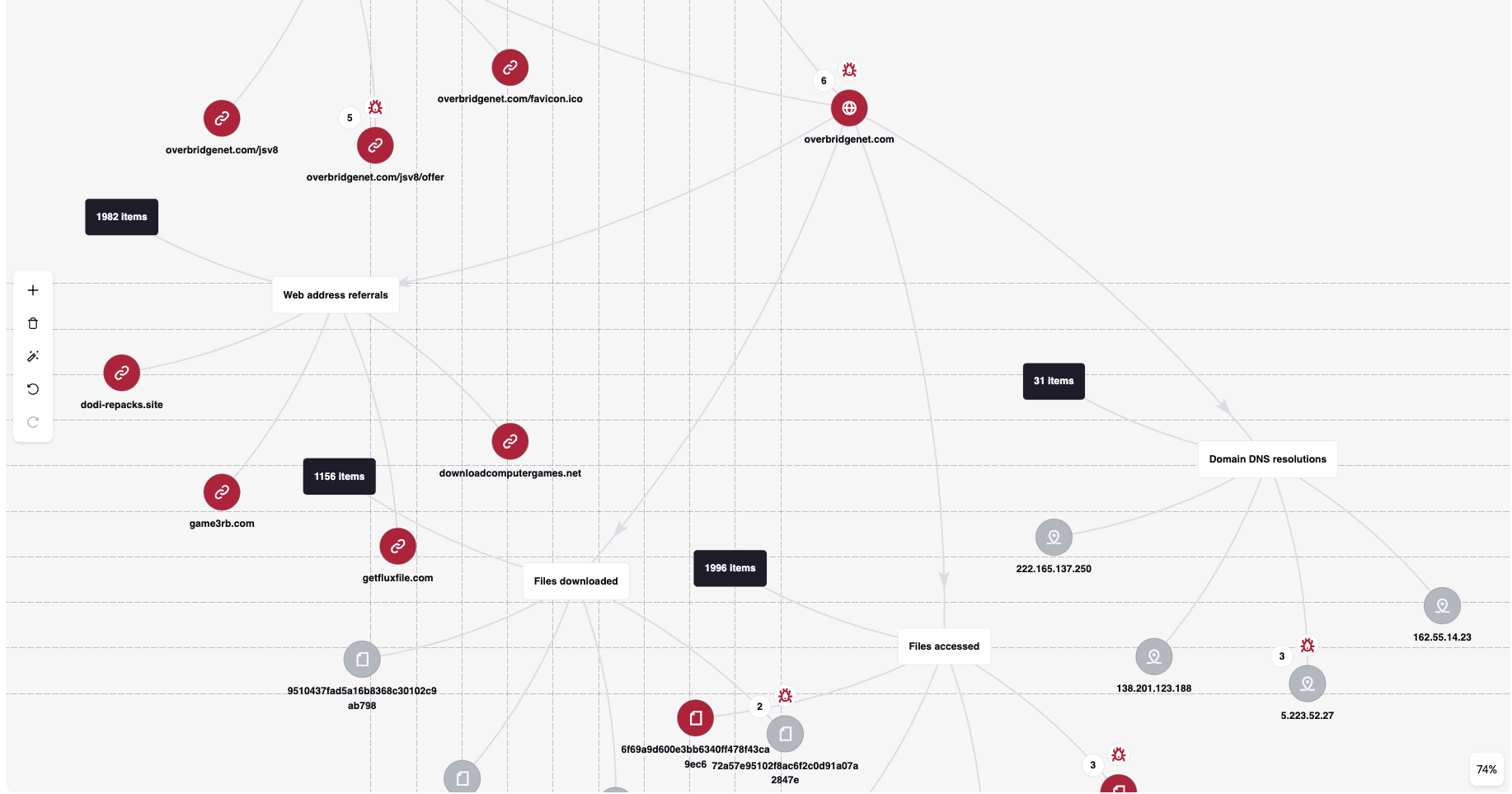
Pivoting and investigative graphs
Modern TI platforms and security data lakes often use graph-style data models to show how indicators, infrastructure, malware and threat actors connect. This makes pivoting feel natural: analysts can jump from one clue to the next, much like a detective following leads. Pivots can take many forms – IP-to-domain, IP to-file hash, beacon-timing patterns, sandbox artifacts and so on. Even a single suspicious domain can provide a lot of details: related C2 infrastructure, hashes of malware, attribution metadata, even previous campaigns. With good automation, a pivot becomes a quick lookup rather than hours of manual research.
Applying Machine-Readable Threat Intelligence (MRTI)
Today’s volume and variety of threat data make automation essential. MRTI structures intelligence so automated systems can easily ingest and correlate it. A lot of vendors provide their feeds in formats such as JSON, CSV, OpenIOC or STIX, which makes it easy for SIEMs, TIPs and SOAR platforms to ingest them automatically.
Indicators such as malicious IPs or domains age quickly – sometimes in only a few hours. The quality of the threat data is just as important as its format. Sharing threat data is a two-way process: the organization gains insights from others and strengthens the community by contributing their own data. The intelligence sharing process varies a lot by industry, regulatory norms and SOC maturity. It can be anything from automated feed updates to full incident reports passed through CERTs.
Enhancing early detection
Perhaps the most transformative impact of TI on SOC operations is the shift from reactive detection to proactive threat hunting and early threat prediction. One way TI improves early detection is by informing detection engineering – the craft of writing analytic rules and signatures.
TI outlines the techniques, tools and patterns adversaries rely on – information that detection engineers can convert into rules and analytics for SIEM, EDR and NDR technologies. So, if intelligence flags a new PowerShell credential-dumping trick used by an APT operating in a customer region, the team can update detections before the attacker even tries it.
A real-world example of leveraging actor-specific intel for early detection is in identifying lateral movement precursors. Suppose TI reveals that a known ransomware group, after initial compromise, runs a specific Active Directory discovery command. The team can add a rule to flag this pattern as potential lateral movement.
Integrating TI into incident response
Actionable threat intelligence doesn’t just enrich detection – it can accelerate investigations and orchestrate some parts of the response via such tools like SOAR/XDR:
- Playbooks can automatically enrich high-severity IOCs.
- Automated checks determine whether an IOC appears across the enterprise (e.g., running YARA scanning across all endpoints).
- Predefined thresholds trigger rapid containment: firewall blocks, host isolation, disabling suspicious user accounts.
Crucially, incidents don’t just get “resolved” – they fuel continuous improvement. TI integration enables a closed-loop feedback mechanism between incidents and the TI database, and establishes a cycle of learning. Every incident produces new data – newly seen phishing senders, C2 IPs and more. In other words, each incident makes the SOC smarter. Retrospective hunting is also key. After an incident, analysts review historical logs to check whether the attacker was active earlier without detection or whether their indicators appear in older data.
TI is one of the simplest and safest parts of automation: it adds context without touching production. Because of that, it’s usually adopted far more readily than other automated actions.
Final thoughts
As we can see, TI, combined with SOC, brings numerous benefits. However, it should be noted that establishing TI is not without challenges. What issues and recommendations should we think about?
- Data overload – there may be too many feeds and not enough prioritization. To solve this issue, check sources and focus on high-value, high-confidence feeds.
- Relevance – often intelligence doesn’t match real organizational risks. To get the best results, tailor TI requirements to your sector, assets and threat profile.
- Data quality – low-confidence or unreliable indicators can do more harm than good. To overcome this obstacle, use trusted providers and double-check feeds before integrating them.
- Skill shortages – limited expertise can result in valuable intel going unused. In such cases, invest in training – from basic lookups to advanced pivoting.
The six questions – what, why, when, how, where and who? – remain the heart of TI, which empowers the SOC not just to monitor – but to understand. Not just to react – but to anticipate. Not just to defend – but to stay a step ahead of the adversary.

Damir Shaykhelislamov is Advanced Threat Protection Solutions Group Manager at Kaspersky.
TNGlobal INSIDER publishes contributions relevant to entrepreneurship and innovation. You may submit your own original or published contributions subject to editorial discretion.
Featured image: SCARECROW artworks on Unsplash
Why small language models may be the greener path for applied AI